Security Operations Center (SOC): Your Shield Against Cyber Threats

Cyber threats evolve every day. Hackers develop new methods to breach networks and steal data. Organizations face constant attacks from ransomware, phishing, and advanced persistent threats. Without proper defense, your business remains vulnerable.
A security operations center provides the protection you need. This dedicated team monitors your systems around the clock. They detect threats before damage occurs. They respond to incidents immediately. They keep your organization secure.
Inventiv Technology delivers comprehensive SOC services designed for modern businesses. Our expert team combines advanced tools with proven processes. We protect your data, systems, and reputation. Our security operations center acts as your first line of defense against cyber threats.
Understanding Security Operations Center Functions
A security operations center serves as the nerve center for organization security. This facility houses security professionals who monitor, detect, and respond to cybersecurity threats. The SOC team works continuously to protect your digital assets and maintain your security posture.
Security operations encompass multiple critical functions. Analysts examine network traffic for suspicious patterns. They investigate security alerts and determine threat severity. They coordinate incident response when breaches occur. They also implement measures to prevent future attacks.
The SOC responsible teams use sophisticated technology platforms. These tools aggregate data from across your infrastructure. Security information and event management systems collect logs. Threat intelligence platforms identify emerging threats. Automation tools speed up response times.
Modern security operations centers differ from traditional IT support. While IT teams fix technical problems, SOC analysts hunt for hidden dangers. They look for indicators of compromise. They track threat actors. They stay ahead of cybersecurity challenges through proactive monitoring.
Monitoring Capabilities
Continuous surveillance forms the foundation of effective security operations. SOC teams watch your systems every hour of every day.
- Real-time network traffic analysis
- Endpoint activity monitoring
- Cloud infrastructure surveillance
- Application behavior tracking
Detection Methods
Advanced threat detection combines multiple techniques. Security operations center teams use layered approaches to find attacks.
- Signature-based threat identification
- Behavioral anomaly detection
- Machine learning analysis
- Threat hunting operations
Response Procedures
Quick incident response minimizes damage from security breaches. SOC responsible teams follow structured protocols during incidents.
- Immediate threat containment
- Forensic investigation
- System recovery coordination
- Post-incident analysis
Intelligence Integration
Threat intelligence keeps security operations current. SOC teams leverage global threat data to strengthen defenses.
- Indicator of compromise tracking
- Threat actor profiling
- Vulnerability intelligence
- Industry-specific threat feeds
Effective security operations require specialized expertise. Analysts need deep knowledge of security architecture and attack methodologies. They must understand how systems work and how criminals exploit them. This expertise takes years to develop.
Organizations benefit from centralized security operations. Instead of scattered security efforts, the SOC provides unified protection. This approach improves visibility across all systems. It also enables faster response and better resource allocation.
Monitoring and Operations Excellence
Security monitoring forms the backbone of every effective security operations center. Continuous observation of your digital environment reveals threats as they emerge. The SOC team maintains constant vigilance over networks, systems, and data flows.Operations teams collect data from countless sources. Firewalls generate logs about blocked connections. Intrusion detection systems flag suspicious activities. Servers record user behaviors. Applications track access patterns. This massive data stream requires sophisticated analysis.
Security operations center analysts use advanced tools to process information. Log management platforms aggregate events from across your infrastructure. These systems correlate data points to identify patterns. They filter noise to highlight genuine threats. This filtering prevents alert fatigue.
Real-time monitoring enables immediate threat detection. When anomalies appear, the SOC team investigates instantly. They determine whether events represent actual dangers or false alarms. Quick assessment prevents threats from escalating into major incidents.

Network Monitoring
- Traffic flow analysis
- Bandwidth utilization tracking
- Protocol anomaly detection
- Unauthorized access attempts
- Data exfiltration monitoring
Endpoint Surveillance
- User activity monitoring
- Process execution tracking
- File system change detection
- Memory analysis for malware
- Registry modification alerts
Cloud Security Monitoring
- Cloud configuration compliance
- API activity surveillance
- Identity and access management
- Resource usage anomalies
- Multi-cloud environment visibility
Comprehensive Vulnerability Management
Vulnerabilities represent weak points in your security architecture. Every system contains potential flaws that attackers can exploit. Effective vulnerability management identifies these weaknesses before criminals discover them. This proactive approach strengthens your organization security defenses.
The security operations center conducts regular vulnerability assessments. Automated scanners examine your infrastructure for known weaknesses. These tools check systems against databases of security flaws. They identify outdated software versions and misconfigurations. They also discover unpatched systems.

Vulnerability scanning provides comprehensive coverage. The SOC team scans networks, applications, and endpoints. They examine both internal and external attack surfaces. Cloud environments receive special attention due to their complexity. This thorough approach ensures nothing escapes notice.
Not all vulnerabilities carry equal risk. Security operations teams prioritize issues based on severity and exploitability. Critical vulnerabilities affecting internet-facing systems receive immediate attention. Lower-risk items get scheduled for routine maintenance. This risk-based approach optimizes resource allocation.
Assessment Process
Systematic vulnerability identification uses multiple scanning techniques and manual testing methods.
- Automated vulnerability scans
- Penetration testing exercises
- Configuration audits
- Code security reviews
- Third-party risk assessments
Remediation Planning
Strategic remediation addresses vulnerabilities systematically.
- Risk-based prioritization
- Patch management coordination
- Compensating control implementation
- Change management integration
- Remediation timeline tracking
Continuous Monitoring
Ongoing vulnerability surveillance ensures new weaknesses receive prompt attention and resolution.
- Real-time threat intelligence
- Zero-day vulnerability tracking
- Compliance monitoring
- Asset inventory management
- Trend analysis reporting
Security Orchestration and Automation
Modern security operations generate overwhelming alert volumes. Manual processing of every event becomes impossible at scale. Orchestration and automation solve this challenge by streamlining security workflows. These technologies multiply the effectiveness of your SOC team.
Security orchestration connects disparate security tools into cohesive systems. Firewalls, endpoint protection, and threat intelligence platforms work independently by default. Orchestration platforms integrate these tools. They enable automated information sharing between systems. This integration improves threat detection accuracy.
Automated Response Capabilities
Security automation executes immediate protective actions when threats appear. These rapid responses limit damage and reduce incident impact.
Key Automation Benefits: Response times drop from hours to seconds. Consistency improves across all incidents. Human error decreases significantly. Analyst burnout reduces through workload management.
- Automatic user account isolation
- Infected endpoint quarantine
- Malicious traffic blocking
- Evidence collection initiation
- Stakeholder notification
- Ticket creation and assignment

Orchestration platforms use playbooks to standardize processes. These playbooks document best practices for common scenarios. Phishing investigations follow consistent steps. Malware incidents trigger appropriate containment measures. Standardization ensures quality regardless of which analyst handles the case.
Advanced Threat Detection and Analysis
Cyber threats grow more sophisticated daily. Attackers use advanced techniques to evade traditional defenses. Effective threat detection requires multiple layers of analysis. The security operations center employs cutting-edge methods to identify hidden dangers.

Threat detection combines several complementary approaches. Signature-based detection identifies known malware and attack patterns. Behavioral analysis spots unusual activities that might indicate compromise. Anomaly detection highlights deviations from normal operations. Together, these methods provide comprehensive coverage.
The SOC team performs continuous threat hunting. Rather than waiting for alerts, threat hunters actively search for indicators of compromise. They hypothesize about potential attack scenarios. They investigate suspicious patterns proactively. This offensive approach finds threats before they cause damage.
Advanced analytics power modern threat detection. Machine learning algorithms process massive data volumes. They establish baseline behaviors for users, systems, and applications. When activities deviate from baselines, analysts investigate. This data-driven approach catches subtle indicators traditional rules miss.
Strengthen Your Security Posture Today
Inventiv Technology's security operations center delivers advanced threat detection and rapid incident response. Our expert team protects your organization 24/7 with cutting-edge tools and proven processes. Don't wait for a breach to prioritize security.
Incident Management and Response
Security incidents require immediate, coordinated action. The security operations center maintains structured incident response processes. These procedures minimize damage and restore normal operations quickly. Effective incident management separates minor disruptions from major breaches.
Incident response follows a proven lifecycle. Detection initiates the process when threats appear. Containment limits threat spread and prevents additional damage. Eradication removes malicious elements from systems. Recovery restores affected services. Post-incident activities extract lessons learned.
The SOC team classifies incidents by severity. Critical incidents affecting core business systems receive highest priority. High-severity events get immediate attention. Medium and low-priority incidents follow standard workflows. This classification ensures appropriate resource allocation.
- Incident Detection and Triage: Security alerts trigger immediate analyst review. Initial assessment determines incident validity and severity. False positives get closed quickly. Genuine threats advance to investigation.
- Containment Strategy Development: Analysts determine optimal containment approaches. They balance security needs against business continuity requirements. Quick containment prevents threat spread while maintaining critical operations.
- Evidence Collection and Preservation: Forensic data collection begins immediately. Logs, memory dumps, and network captures preserve evidence. This information supports investigation and potential legal proceedings.
- Threat Eradication: Once contained, malicious elements get removed systematically. Compromised credentials are reset. Malware gets deleted. Backdoors are eliminated. Thorough eradication prevents reinfection.
- System Recovery and Validation: Affected systems return to operation after cleaning. Security operations teams verify complete threat removal. They test system functionality. They monitor closely for signs of persistent compromise.
- Post-Incident Review: After resolution, the SOC team analyzes the incident. They document timeline and actions taken. They identify improvement opportunities. These lessons strengthen future defenses.
Security-Focused Change Management
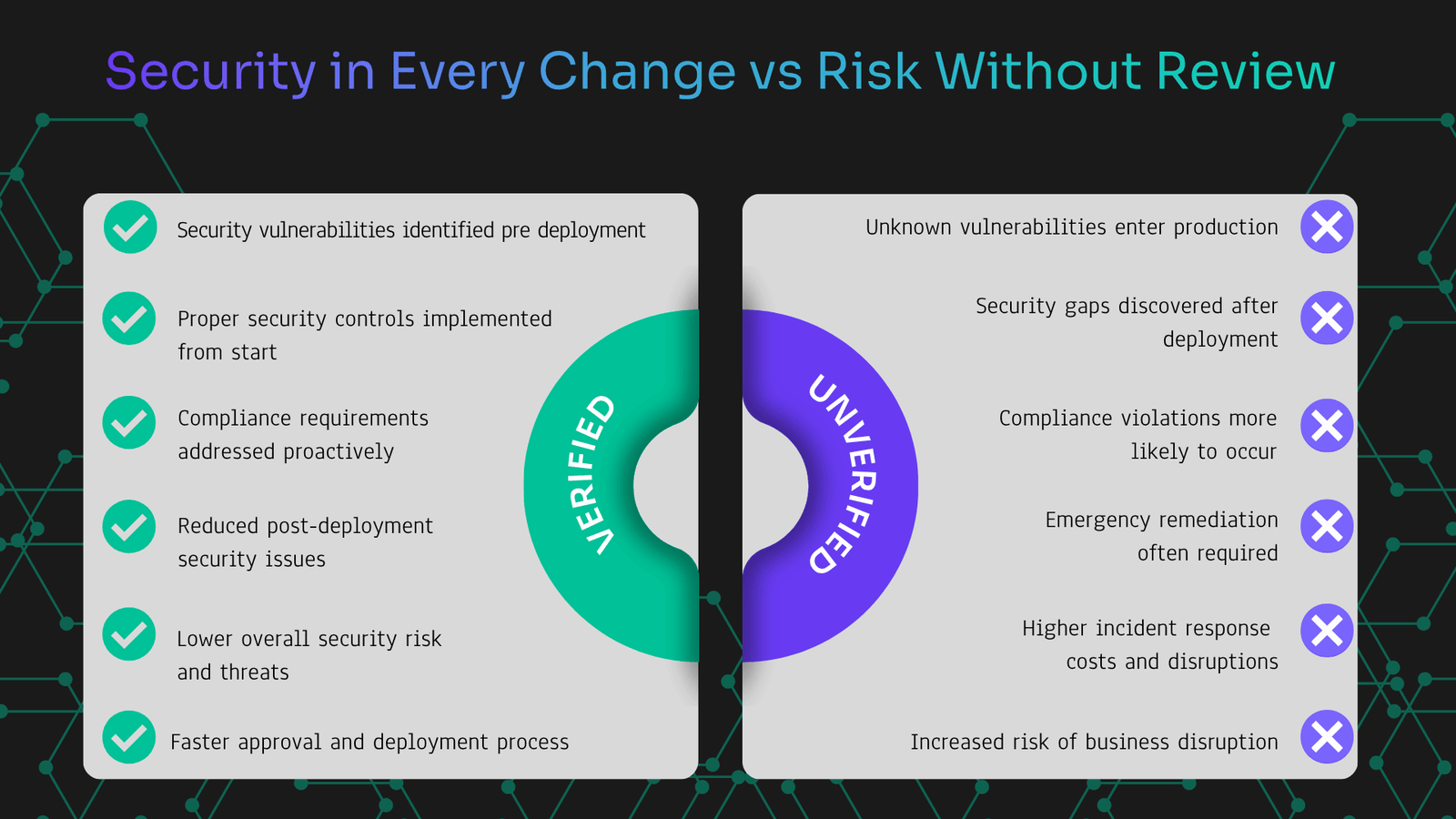
Changes to IT infrastructure introduce security risks. New applications might contain vulnerabilities. Configuration modifications can create security gaps. The security operations center integrates security into change management processes. This integration prevents changes from weakening organization security posture.
Change management processes require security architecture consideration. New systems must align with security standards. Network segmentation principles need respect. Access controls require proper configuration. The security operations center ensures architectural integrity during changes.

Business Benefits of Security Operations Center
Investing in a security operations center delivers substantial business value. Beyond technical security improvements, SOC services provide strategic advantages. Organizations gain competitive edge through superior cybersecurity capabilities. These benefits extend across all business functions.
Risk reduction stands as the primary benefit. Cyber threats pose existential risks to modern businesses. Data breaches cost millions in remediation and reputation damage. Ransomware attacks halt operations completely. The security operations center prevents these catastrophic outcomes. Prevention costs far less than incident recovery.
Compliance requirements become manageable through security operations. Many regulations mandate continuous monitoring and incident response capabilities. The SOC team maintains necessary documentation. They implement required controls. They generate compliance reports. This support simplifies regulatory adherence.
Financial Protection
Security operations deliver measurable financial benefits through risk reduction and efficiency gains.
- Reduced breach costs
- Lower cyber insurance premiums
- Avoided regulatory fines
- Prevented revenue loss
- Decreased incident expenses
Operational Excellence
SOC services enhance operational efficiency across technology and business processes.
- Improved system uptime
- Faster incident resolution
- Better resource utilization
- Streamlined security processes
- Enhanced team productivity
Strategic Advantage
Superior security capabilities provide competitive advantages in the marketplace.
- Customer trust strengthening
- Partner confidence building
- Market differentiation
- Contract requirement satisfaction
- Brand reputation protection
Partner with Inventiv Technology for Complete SOC Services
Protecting your organization requires expert security operations. Inventiv Technology delivers the comprehensive SOC services you need. Our team stands ready to strengthen your defenses against cyber threats. Take the first step toward robust security today.
Stay ahead of cyber threats with proactive security operations. The threat landscape evolves constantly. Reactive security no longer suffices. Organizations need continuous monitoring and rapid response. Inventiv Technology provides these essential capabilities.Improve your organization security posture starting today. Every day without comprehensive security operations increases risk exposure.The time to act is now.

Start Your Security Operations Journey Today
Contact Inventiv Technology to discuss your security operations needs. Our specialists will assess your environment and recommend tailored solutions. Protect your organization with industry-leading SOC services backed by expert analysts and advanced technology.

